Key takeaways
- Use social listening to drive strategy, not just reporting. Go beyond tracking brand mentions. Leverage real-time insights to shape messaging, improve customer experience, and inform product development.
- Tie listening efforts to clear business goals. Whether it’s boosting brand awareness, improving response times, or identifying market gaps, define SMART goals and measure success with metrics like share of voice, sentiment, and engagement.
- React fast—then optimize. Spot trending topics, negative sentiment, or potential crises early. Use those insights to adapt your content strategy, improve customer support, and stay one step ahead of competitors.
Social listening is not just about tracking likes or retweets. Smart marketers use it to understand customer needs, spot industry trends, and boost brand awareness. Think of it as eavesdropping (the ethical kind!) to uncover invaluable audience insights that can become the basis of an effective, customer-focused marketing strategy.
More than 60% of US businesses already use social listening tools to monitor brand mentions and customer sentiment… because it works. From catching a pricing error before it tanks your brand reputation (hello, Hong Kong Airlines’ 4,900% engagement win) to shaping new product ideas based on customer feedback, social listening delivers actionable insights that inform everything from messaging to content strategy.
Ready to make it work for you? This guide breaks down the benefits of social listening, walks you through building a social listening strategy, and shares tips for optimizing your efforts.
Social listening (sometimes called social media monitoring) is the practice of tracking social media platforms, websites, forums, and even podcasts to understand what people say about your brand name, competitors, or industry. It’s like having a front-row seat to real, relevant conversations across social networks and social media channels.
Here’s why social listening is a must for your social media strategy:
- Stay on-trend. Social media listening tools can help you spot trending topics and keep your branded content culturally relevant.
- Improve customer experience. With social listening, you can catch pain points early and improve your processes accordingly, boosting satisfaction and customer support outcomes.
- Guide product development. You can build an entire product roadmap informed by customer feedback, turning ideas into hits.
- Protect brand reputation. Social listening allows you to spot negative sentiment or potential crises fast — and react immediately (sometimes even turning these situations into publicity wins).
- Prove ROI. With global ad spend expected to exceed 276 billion dollars in 2025, social listening can help advertisers get more bang for their buck. It ties insights to metrics like engagement, share of voice, and sentiment, showing how your marketing campaigns deliver on business goals.
Here’s how Brian Wright, Head of Social Listening at Wells Fargo, summed it up in a conversation with eMarketer: “Social listening provides real-time insights for strategic decision-making, especially during change.”
TL;DR: social listening is your ticket to smarter marketing campaigns and stronger brand monitoring.
Ready to turn your social media analytics into action? Here’s a clear, actionable plan to create a social listening strategy that aligns with your business goals. Whether you’re tracking TikTok trends, engaging in influencer marketing, or managing customer support, this template works across multiple use cases.
Step 1: Set clear goals
Start by asking: What do you want to achieve? Your social listening strategy should tie to specific business goals.
Want to boost brand awareness? Monitor share of voice. Need to optimize customer experience? Track negative sentiment.
Here are the common use cases for social listening:
- Brand monitoring: Track mentions of your brand to gauge sentiment.
- Competitive analysis: Spy on competitors’ hashtags or pain points to find market gaps you can fill.
- Product development: Gather feedback for new and improved products.
- Crisis management: Spot potential crises in their early moments, and address them before they cause substantial damage.
- Social media marketing: Strengthen content creation efforts by understanding what resonates.
Use SMART (specific, measurable, achievable, relevant, time-bound) goals to stay focused. For example, “Increase positive sentiment by 10% in Q1 by responding to 90% of customer mentions,” is a well-formulated goal.
Step 2: Pick the right social listening tools
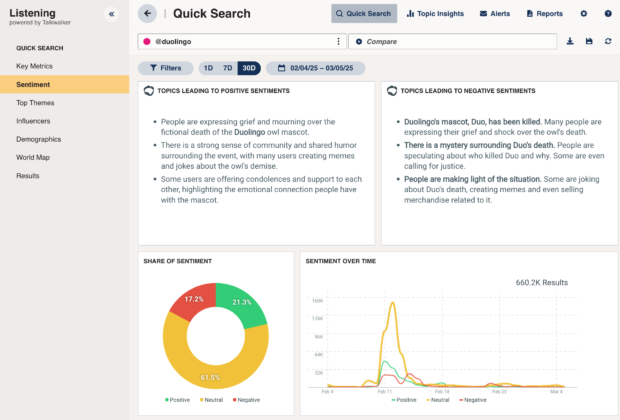
You don’t need to scroll through tweets manually — social listening platforms automate the process. Hootsuite Listening offers easy-to-use features like sentiment analysis, real-time alerts, and integrations with your social media management system.
Wondering how to choose a social listening tool? Here’s what to look for:
- Coverage: Ensure it tracks key social platforms (including video-based networks like TikTok and YouTube), websites, forums, and emerging spaces like podcasts.
- Features: Look for competitor analysis, hashtag tracking, influencer monitoring, and AI-powered insights.
- Price: Many tools offer free trials. Start small and see what you like — then, scale up.
Psst: We might be biased, but we believe that Hootsuite and Talkwalker are your best bet. Need proof? Read about how an NBA team leveraged Talkwalker for a 352% video view boost.
Step 3: Set up your queries
Keywords are the heart of social media monitoring.
All social listening tools will allow you to track relevant keywords like your brand name, product names, or industry terms.
If you want to get more granular in your snooping, use Boolean logic in your queries:
- Broad queries: “brand name” OR “brandname” (cover misspellings).
- Sentiment filters: “brand name” AND “love” OR “hate”.
- Competitor queries: “competitor name” AND “fail” OR “issue”.
You can also include hashtags, emojis, or slang in your tracking, especially for TikTok or Snapchat. Influencer mentions and online conversations from niche communities can offer valuable insights too.
Bonus: Try our free (no sign in required!) Boolean query generator to get started!
Step 4: Analyze the data
Data is only useful if you act on it.
To make this task easier, sort your social listening insights into buckets:
- Sentiment: Are mentions of your brand positive, negative, or neutral?
- Trends: What hashtags or topics are trending?
- Pain points: Are there recurring complaints in your brand and product mentions?
- Opportunities: Can you spot customer needs none of your competitors are addressing?
But how do you action this data on a regular basis?
This depends on the trends you’re seeing. If you see tweets about slow shipping, loop in customer support. If a hashtag goes viral, create content to join the conversation.
Monitor forums for niche sentiment shifts and use those learnings to adjust messaging or launch new products.
Step 5: Measure and optimize
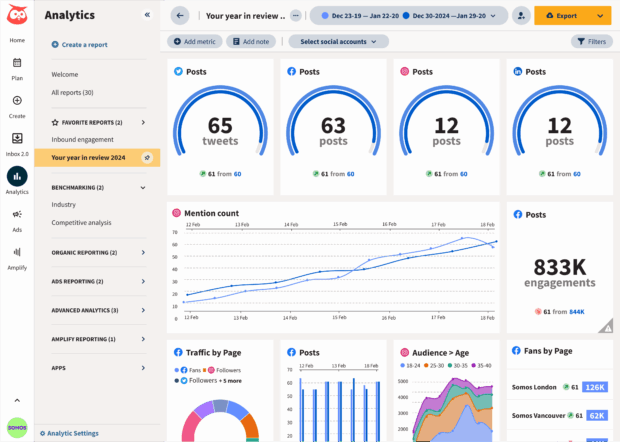
The key to making analytics work for you rather than create extra work for you is to track metrics that matter to your goals.
Common metrics for social listening include share of voice, sentiment, response rate, engagement, and influencer impact.
Use social media dashboards to visualize your performance and share key results with stakeholders.
You might also want to adjust your queries monthly to stay relevant — new trending topics and hashtags pop up fast.
Social listening examples: Real wins from real brands
Need proof that social listening works? These case studies show how brands turned insights into results
- NBA team: Used Talkwalker to analyze fan emotions, boosting video views by 352% and impressions by 46%. A 27% engagement lift across all social channels justified hiring a full-time social media lead.
- Hong Kong Airlines: Caught a pricing error via social media monitoring, fixed it fast, and saw a 4,900% engagement spike, turning a crisis into a PR win.
- HelloFresh: Tracked influencer mentions with Talkwalker, informing recipe and packaging tweaks that optimized marketing campaigns and proved ROI.
- Pharmaceutical company: Listened to MS patient conversations, leading to better support programs and messaging.
- Yves Rocher: Used social listening data to align product messaging with customer values like sustainability, strengthening brand reputation.
- Deutsche Telekom: Built a crisis response hub with Talkwalker for real-time brand monitoring, catching potential crises early.
These brands show that social listening isn’t just about collecting data. It’s also a helpful tool for more advanced content creation, customer support, and market research.
Want to stand out? These tips, inspired by real-world wins, will supercharge your social listening strategy.
Hack #1: Build a sentiment template
Create a playbook for responding to positive, negative, or neutral mentions. This will help your team scale response rates — and lower response times.
Hack #2: Consistently monitor competitors
Track competitors’ brand mentions, hashtags, or pain points. Spot their weaknesses (e.g., slow customer support) and position your brand as the fix.
Bonus: You’ll catch industry trends early using social media monitoring tools that surface relevant social media conversations and demographics data.
Hack #3: Set influencer alerts
Track mentions from influential accounts, like HelloFresh did, to tap into high-stakes conversations and validate your marketing efforts. The meal kit delivery service set up real-time alerts for callouts from authors with more than 10,000 followers to never miss an opportunity to connect with an engaged target audience.
Tip: For authentic reach, engage microinfluencers — Gen Z trusts them most.
Social listening is moving fast. Valued at $8.44 billion in 2024, it’s projected to hit $16.19 billion by 2029. Add to this the new spaces (like podcasts and AI-generated content) gaining traction with online audiences, and the math is clear — the brands that listen will win.
Irina Novoselsky, Hootsuite’s CEO, says:
Organizations that systematically capture and analyze social conversations feel more confident in their social ROI. The split is clear. Some still have to defend social in every board meeting, while others shape product roadmaps and forecast market shifts with customer intelligence.
So, if you’re ready to boost your social engagement, and turn deep insights into new social media posts and measurable business results — give social listening a try today.
Checklist for getting started
Ready to dive into social media listening? Here’s a quick checklist to kick things off:
- Pick a goal: Start with one, like tracking brand mentions or competitor analysis.
- Choose a tool: We recommend Hootsuite Listening. (Grab your free trial here!)
- Set up queries: Use relevant keywords, hashtags, and sentiment filters.
- Act on insights: Respond to customer feedback, join in on trending topics, or fix pain points.
- Track metrics: Measure engagement, impressions, or share of voice to illustrate the impact of your strategy.
Hootsuite makes it easy to monitor keywords and conversations on social media, so you can focus on taking action on the insights available. Try it free today.