Ready to grow your business with an audience of Snap-hungry millennials and Gen-Zers? Learn how to use Snapchat to your full advantage and drive more brand engagement, awareness, and revenue. We’ve got you covered every step of the way.
Table of Contents
Bonus: Download a free guide that reveals the steps to create custom Snapchat geofilters and lenses, plus tips on how to use them to promote your business.
What is Snapchat?
Snapchat is a visual social media platform where users can share fleeting pictures and videos.
After launching in 2011 and releasing the Stories function in 2013, Snapchat has grown to become one of the top social media platforms in the world. And like Shakira’s hips, the Snapchat stats don’t lie. As of July 2021, the platform has 293 million daily active users—a growth of 23% year on year.
Nowadays, Snapchat gives you the power to record and share live videos, locate friends on an engaging map, experience augmented reality (AR), and much more. Pretty cool, huh?
New features are at the forefront of what makes Snapchat a unique tool for business owners and regular users alike.
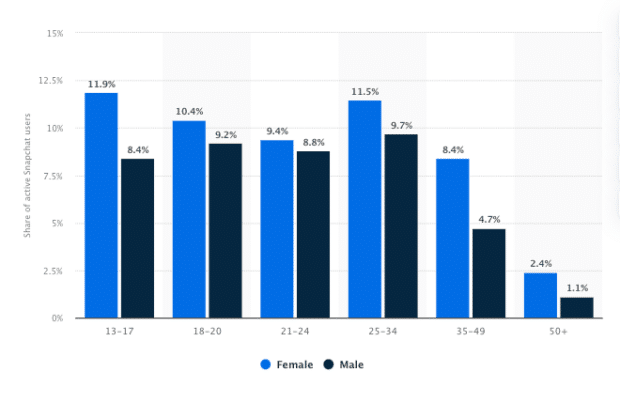
It’s clear that Snapchat firmly has a seat at the table of social media giants—even if its users’ demographic skews more toward the Millennial and Gen-Z cohorts.
Source: Statista: Distribution of Snapchat users worldwide as of July 2021, by age and gender
If your target audience is under 34, Snapchat might be the perfect platform for your business—especially if you operate in the direct-to-consumer market. A huge 60% of Snapchat users are more likely to make impulse purchases, which signals that the platform can increase your sales, drive more revenue, and translate to a positive return on investment (ROI).
Snapchat features and terminology
Snapchat is brimming with features that will help you drive audience engagement and build brand awareness. But first, let’s take a look at some key Snapchat terminology.
Snap
Available to all users since day one, a Snap is a picture or video that you send through the app to one or more of your friends.
A video snap can be a maximum of 60 seconds long (known as a Long Snap). Keeping in line with the app’s original feature, Snapchat doesn’t hold onto any photo or video content—the platform deletes content after the recipient has viewed the Snap.
Stories
Stories are Snaps that you’d like to share with all your Snapchat friends. Stories stay on the app for 24 hours before being deleted. If you’d like to save your Story, you can download them to your device’s camera roll or save them to Memories.
Custom Stories
Custom Stories allows you to create Stories together with other people from your friends’ list.
Snapstreak
A Snapstreak (or Streak) tracks how many consecutive days you and a friend share Snaps. You’ll see a flame emoji next to your friend’s name, with a number indicating how many days you’ve kept the Streak going.
Filter
A Snapchat filter is a fun way to jazz up your Snaps by adding an overlay or other special effects. Filters can change based on special events or holidays, location, or time of day.
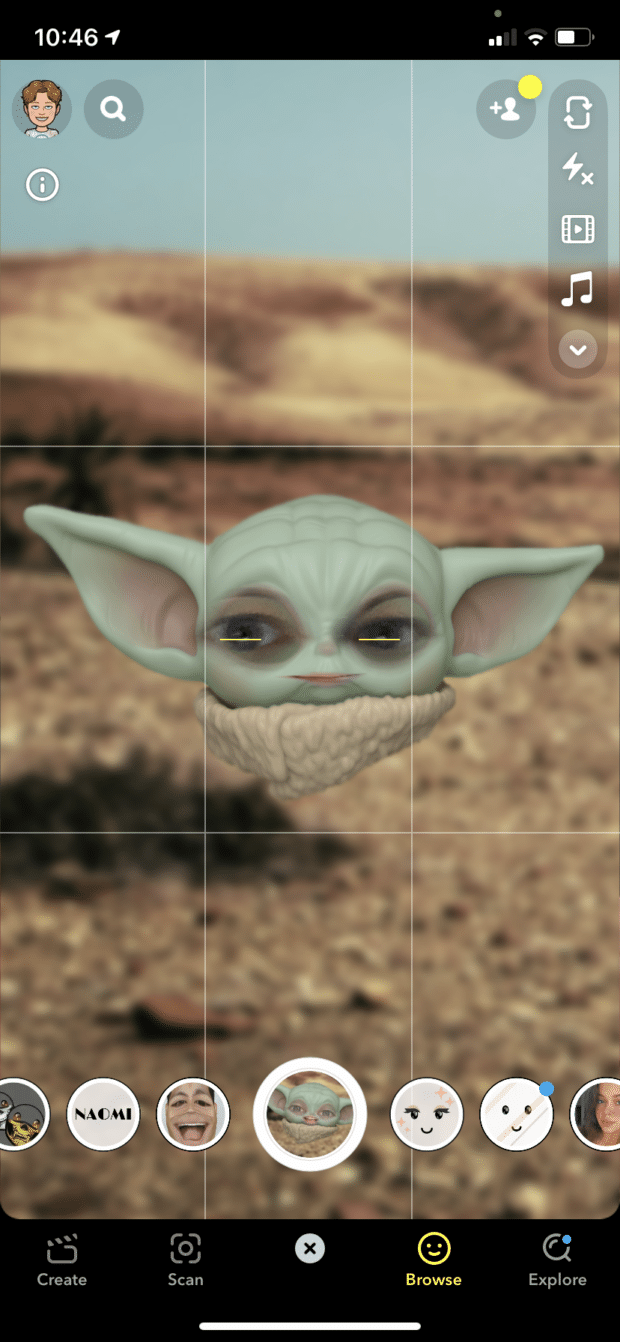
Lenses
Lenses are where AR comes into play. Snapchat Lenses allow you to add 3D special effects, objects, and characters to your photos or videos. Unlike filters, you use lenses while you are taking a Snap.
Geofilter
Similar to Filters, Geofilters are unique to your current location. To enable Geofilters, you have to turn on your location in Snapchat. You can also create a custom Geofilter for as little as $5—great for building brand awareness or showcasing an event.
Snapcode
Snapcodes are unique QR-style codes that you scan to add friends or access features and content on Snapchat. Each user is automatically assigned a Snapcode, and you can create additional Snapcodes that link to any website.
Chat
Chat is Snapchat’s version of instant messenger for individual and group chats. Messages disappear after they’re viewed.
Memories
Memories are Snaps and Stories that you can save for viewing later, rather than allowing them to disappear. Think of Snapchat Memories as your personal photo album that you can view anytime.
Friends
Friends are people who you’ve added on Snapchat (or they’ve added you!) You can share Snaps, Stories, and other content with your friends’ list.
Discover
Discover is a Snapchat screen where brands share Stories with the app’s large audience. Perfect for businesses, publishers, and content creators looking to increase engagement and build brand awareness. 
Snap Map
Snap Map shows your location and the locations of all of your friends. You can view Snaps submitted to the Snap Map from across the world. Of course, if you don’t want to share your location, you can always put yourself in Ghost Mode.
Context Cards
Context Cards use information from Snapchat’s partners to provide additional information about a place mentioned in a Snap or allow you to take actions like booking a ride or reserving a table for dinner. You can access Context Cards by swiping up on a Snap or Story.
Bitmoji
A Bitmoji is a cartoon avatar that represents you. Fully customizable in the Snapchat app, Bitmoji allows you to add personality to your profile and account.
Cameo
Not to be confused with the celebrity messaging app of the same name, Snapchat Cameos are animated gifs that you can customize with your face and send to friends.
Spotlight
Snapchat’s Spotlight feature is the place to share video content with a public audience. Like TikTok and Instagram Reels, Spotlight allows users to post 60-second videos to the app’s Spotlight section. Think of Spotlight as a place to share your best content in the hope that it goes viral.
https://twitter.com/Snapchat/status/1330873747335733251
Snapcash
Powered by Square, Snapcash is a fast, free, and easy way to send money to your friends via the Snapchat app.
How to set up a Snapchat for Business Account
To execute any marketing campaigns on Snapchat, you’ll need to register for a Snapchat business account. The process takes seconds, and we’re here to help you at each step.
1. Download the free Snapchat app
Go to the App Store (for Apple iOS) or the Google Play Store (for Android) and download the app to your device.
2. Create a regular Snapchat account
Before you set up a Business account, follow these steps to create a regular account:
- Open the Snapchat app and tap Sign Up. Next, enter your first and last name and tap Sign up & Accept.
- Enter your birthday and tap Continue.
- Create a username that represents your company. Snapchat will suggest available usernames if the one you choose isn’t available. We recommend choosing a username that you won’t regret later; the only way to change your username is to create a new account. Tap Continue.
- Create your password and tap Continue.
- Enter your email address and tap Continue.
- Enter your phone number and tap Continue. Snapchat will send a verification code to your mobile phone. Enter this when prompted, and Snapchat will verify your account.
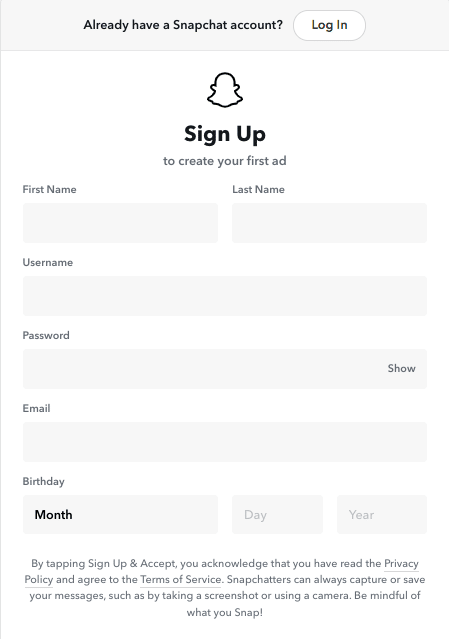
3. Register for a Business Account
Now that you’ve set up a personal Snapchat profile, you can register a Business Account. To do so, follow these steps:
- Head to the Snapchat Ads landing page on your device or computer.
- Tap Create an account, and it’ll take you to the following screen.
- Because you’ve already created an account, tap Log In at the top of the screen and enter your username or email and password for the account you just created.
- Enter your business name, email address, and name. Tap Next.
- Add the primary location that you conduct business.
Now you’re all set to start using Snapchat for marketing purposes!
If you’re familiar with other social media apps, navigating Snapchat should come easily to you.
If you’re unsure, we’ve broken down each screen, how to access them, outlined their purpose, and set you on the right path for learning how to use Snapchat to its full potential.
Camera screen
Think of the camera screen as your home screen. Here, you can take Snaps, send Snaps, and navigate to other areas of the app:
- Swipe left for the Chat Screen.
- Swipe right for the Stories Screen.
- Swipe up for the Memories Screen.
- Swipe down for the Search Screen.
On the right side of the Camera Screen is a toolbar. Here, you can control camera settings such as flash, switch between front or back-facing camera, set a self-timer, adjust the focus settings, and add a grid to your camera screen for more accurate Snapping.
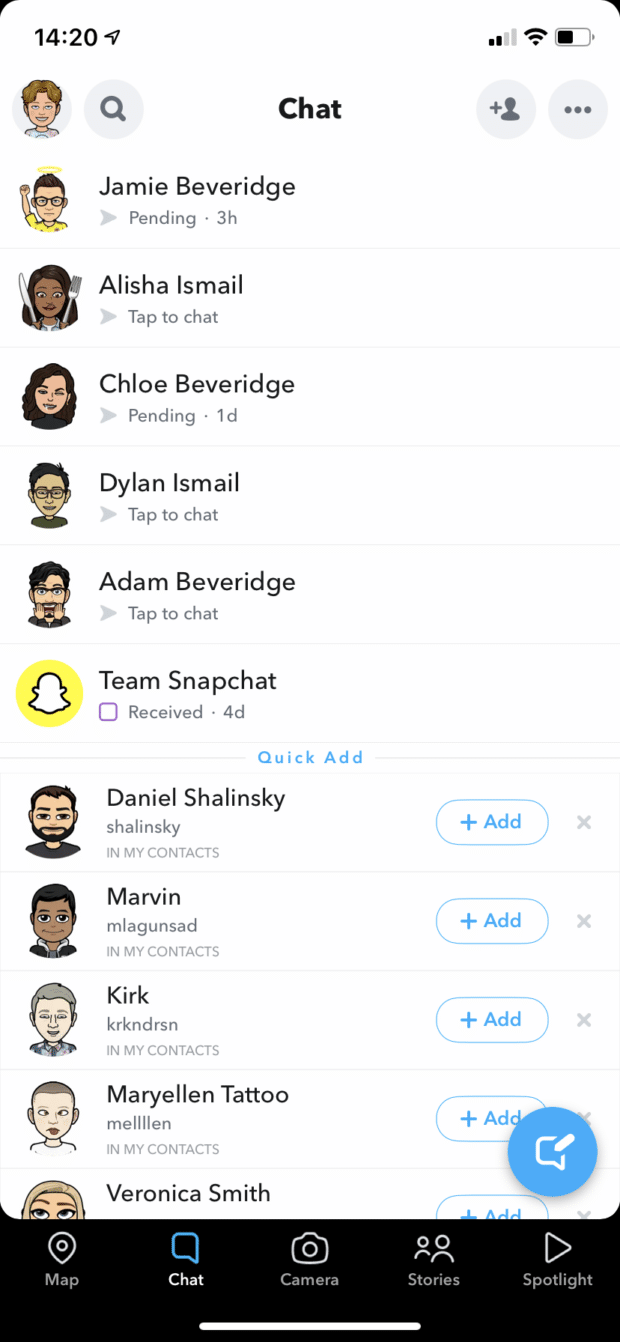
Chat screen
The Snapchat Chat Screen is where you’ll find “everything that has to do with your friends.” Here, you can chat with friends, view Snaps that they’ve sent you, edit your friend’s list, and make audio and video calls.
How to use Snapchat’s Chat feature
Snapchat’s Chat feature allows you to connect with friends one-on-one or have a group chat with several people. For individual chats, messages delete automatically once you both leave the conversation. Group chat messages are also deleted after 24 hours.
If you don’t want a message to disappear, you can press and hold it to save. Keep in mind that other people in the chat will see that you’ve done so since the background of the message will turn gray.
How to chat with one friend
To get a conversation going with a friend, tap their name on the Chat Screen, or tap the blue icon in the bottom right corner and select the friend you’d like to start chatting with.
How to start a group chat
To chat with multiple friends, tap the blue icon in the bottom right corner, select the friends you’d like in your group chat, and then tap Chat.
How to add friends on Snapchat
Snapchat without friends is like going to a party and being the only person in the room—dullsville! To get the most out of Snapchat, you’ll need to add new friends. You can add people you know from your contacts, but Snapchat gets a whole lot more engaging when you branch out a little. Here’s how:
Add by Snapcode
To add a friend using Snapcode, simply open Snapchat, point the Snapchat camera over the other user’s Snapcode, then tap Add Friend.
Add by Name
On Snapchat, you can search for and add friends by their real name or username. Tap the magnifying glass on the top left of the Chat Screen, and type in who you’re looking for. Then, if they’re using Snapchat (and have a public profile), you can add them as a friend.
Quick Add
Snapchat’s Quick Add feature is similar to suggested contacts on other social media apps. The feature suggests people you may want to connect with based on your mutual contacts, as well as the contacts on your phone.
To use the Quick Add feature, open the Chat Screen, and a list of users will appear in the lower half. Tap the +Add button next to the user you want to add as a friend.
You may not see names suggested in Quick Add until you have started to build up your Snapchat network.
How to accept a friend request on Snapchat
When another user sends you a friend request on Snapchat, you have to accept it before you are connected. To accept a friend request,
- Open Snapchat and tap on the Profile circle on the top left of the screen
- Tap Added Me.
- Tap the + button next to your friend’s username to accept their friend request
Profile screen
In the upper right corner of the camera screen is an icon with your Bitmoji (if you’ve set one up). Tap this to access your profile screen. You can find a collection of your Snapchat information on this screen, e.g., your account info, Bitmoji, location on the Map, Story management, and more.
Stories screen
Swipe right to access the Stories screen. Here, you’ll find your Stories, your friends’ Stories, and Stories from brands and creatives in the Discover section.
To move through Stories, simply tap the screen, and the app will automatically move to the next Snap in the Story. When a Story ends, Snapchat will automatically move on to the next Story. Easy!
Need a bit more guidance? We’ve detailed exactly how to create a Snapchat Story a bit further down this post.
Memories screen
Who doesn’t love looking back on cherished memories? Luckily, this nifty Snapchat feature allows you to swipe up from the camera screen and revisit Snaps and Stories from days gone by.
Flick between your Snaps, Stories, Camera Roll, and private Snaps along the main menu at the top of the screen.
How to use Snapchat Memories
Snapchat Memories allows you to save Snaps and Stories to view them later or even repost them.
You can save any Snap to Memories by tapping the Save button. You can also choose to save all Snaps to Memories by default.
Open the Snapchat app and swipe up or tap the small circle below the capture button to view your Memories.
Want to know more about what you can do with Snapchat Memories? We’ve got a post on how to use Snapchat Memories to grow and engage your audience.
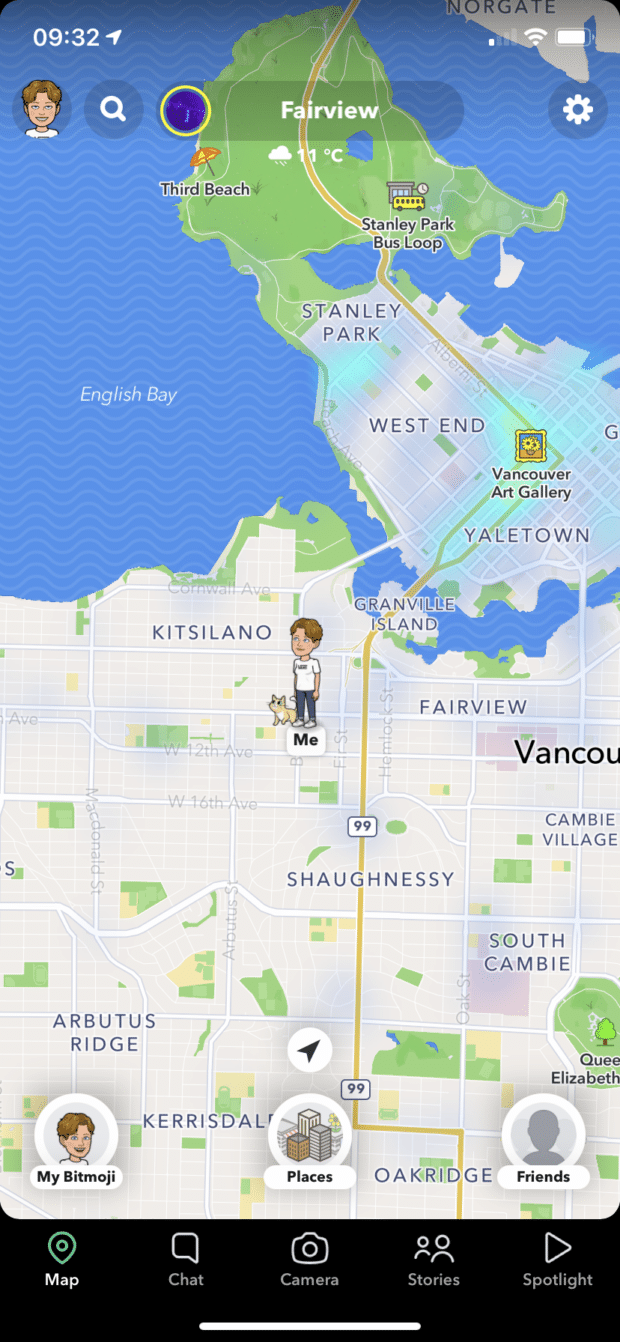
Map screen
Possibly the coolest feature on Snapchat is the Snap Map. On this screen, there are a few things you can do:
My Bitmoji
Bitmoji is all about showing the world your personality. On the Snap Map, you can change your Bitmoji to reflect what you’re up to. For example, if you’re at a club getting your dance on, change your Bitmoji to one of you poppin’ some moves! Or, if you’re hard at work at a local coffee shop, update your Bitmoji to reflect you sipping on a brew.
Places
See what’s going on around you by tapping the Places icon on the bottom of the Map screen. The Map will come to life and show you popular spots near your location. Click on a location to access details, such as opening times, popular times to visit, and contact information. You can even send place recommendations to your friend list.
Friends
Tap the Friends icon on the Snap Map to locate your friends. You can also see places they’ve been to as well as engage with Snaps at different locations across the world!
Search screen
Swipe down on the camera screen or tap the magnifying glass in the top left corner to access the Search screen. Here, you can search Snapchat, access games, quickly add friends, and check out what’s currently trending on Snapchat.
Spotlight screen
Access the Spotlight Screen by tapping the triangle icon on the Camera screen’s lower menu. This screen is the place to find and interact with short viral videos from across the platform.
- Tap the heart button to favorite a Spotlight video
- Tap the arrow button to send a Spotlight video to a friend
- Tap the three dots button to subscribe to the creator’s content or report inappropriate content
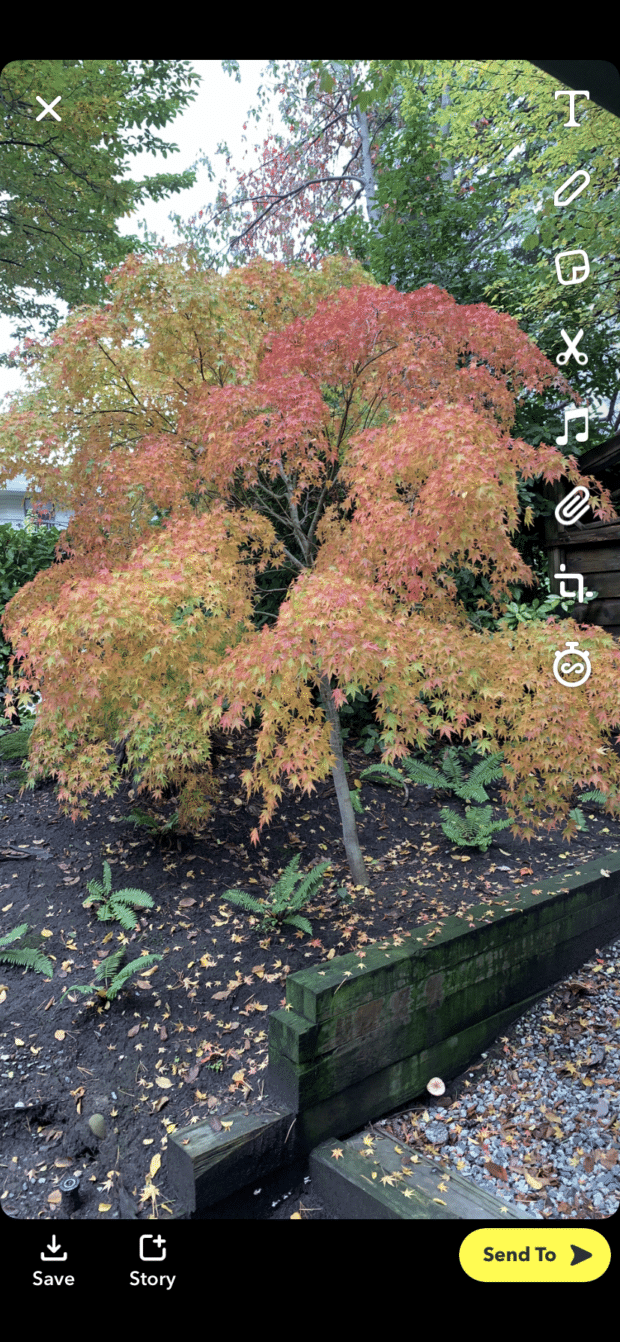
How to create a Snap
Sure, viewing Snaps is fun, but you’ll also need to know how to create Snaps of your own. When you open the Snapchat app, it goes directly to the camera screen, so you’re all set to start Snapping.
1. Take a picture or video
To take a picture, tap the round capture button at the bottom of the screen.
Hold the capture button down to take a video, and a red marker will appear to indicate that that app is recording. You can capture up to 10 seconds of video in one Snap. If you keep holding the button down, it will record multiple Snaps up to 60 seconds of video.
To take a selfie, flip the camera on your screen by tapping the square arrows icon in the top right corner or double-tapping anywhere on the screen. If you don’t like the photo or video, tap the X icon in the top left corner to discard and try again.
2. Get creative
Once you take your Snap, it’s time to unleash your creative side! You can dress up your Snap with innovative tools and filters.
Creative Tools
The following creative tools appear on the right of your screen:
- Caption (T icon): Add text, complete with bold, italics, or underline styles. You can also use the @ symbol to mention friends in your Snaps.
- Doodle (pencil icon): Snapchat’s drawing tool. You can change the color and size of your brush or tap the heart icon to draw with emojis.
- Stickers (a square icon that resembles a sticky note): Add stickers from the Snapchat library.
- Scissors (scissors icon): You can select just about any part of a Snap to turn it into a sticker you can use on your current Snap or save for the future.
- Music (music note icon): Tap the music icon to add the hottest jams to your Snap. You can browse by playlists, search for specific artists or songs, and edit the music snippet you want on your Snap.
- Link (paperclip icon): Tap this icon to enter the URL of any webpage. When your friend views your Snap, they can swipe up to find the linked webpage.
- Crop (two right angles icon): Tap this to crop and zoom in or out of your Snap.
- Timer (stopwatch icon): Select the amount of time that your Snap will be viewable—up to 10 seconds. Or, choose the infinity symbol to let your friends view the Snap for as long as they like.
You can also add filters and lenses—more on this below!
3. Send your Snap
Once your Snap is ready to go, click the yellow Send To arrow icon on the bottom right of the screen. Then, select which contacts you’d like to send the Snap to by checking the boxes beside their names. You can also add your Snap to your Story and your Snap Map.
Once your Snap is sent, the app will take you to the Chat Screen.
To send multiple Snaps, repeat the process above. Your friend will receive your Snaps in the order you sent them.
How to view a Snap
You now know how to create and send a Snapchat. But, do you know how to view Snaps? It’s easy:
- Swipe right from the camera screen to open the Chat screen.
- If friends have sent you Snaps, you’ll see an icon next to their username. Depending on the type of message sent, the icon will vary in color:
- Blue: a Chat message with no Snap attached
- Red: a Snap, or multiple Snaps, will play in sequence without audio
- Purple: a Snap, or multiple Snaps, will play in sequence with audio (Pro tip: If you’re viewing Snaps in public, turn your media volume off and view them in silence—or wait and watch them later.)
- Tap on the message to open it. If you’ve been sent multiple Snaps from the same friend, you’ll view them in sequence. The outer ring of the timer shows you how much time is left in the current Snap. Tap once to skip to the next message or swipe down to exit the Snap.
- Replay the Snap. Tap and hold down your friend’s name, then tap the Snap to view it again. Don’t leave the Friends screen, or you won’t be able to replay the Snap.
- Take a screenshot (if you dare). You can take a screenshot of Snaps that people send you (the same way you usually would on your phone). However, Snapchat will notify the person who sent you the Snap that you took a screenshot.
Note: You can also set up push notifications on your phone for new Snaps.
How to create Snapchat Stories
A Snapchat Story is a collection of Snaps captured within the past 24 hours. By default, your Story is visible to all of your friends, and they can view the Snaps in your story as many times as they like. You can limit who sees your Story by changing your privacy settings.
How to create and edit your Story
Add Snaps to your Story
Follow the instructions we’ve detailed above on creating a Snap, then tap the Story button at the bottom left of your screen. Finally, tap Add, and the Snap will become part of your Story.
Delete a Snap from your Story
From the camera screen, tap the circular icon in the very top left of the screen (you should see your most recent Snap there). Then tap My Story. Tap any Snap to view it, tap the three dots in the top right corner, and tap Delete Snap.
Save your Story
Remember, your Story is a rolling archive of the past 24 hours. If you’d like to hold on to a Story longer than that, you can save it. From the camera screen, tap the profile icon in the top left corner, then tap the download button beside My Story to save your current Story to Memories or your camera roll.
See who’s viewed your Story
Tap the eye icon on any Snap within a Story to see who’s viewed it. (Pro tip: You can only find out how many people viewed your Story while it’s live. Once it’s disappeared, so does the view tracking.)
How to view someone’s Story
From the camera screen, tap on the Stories icon in the bottom right corner. You’ll see a list of contacts who’ve updated their stories. To view the Story, tap on your friend’s username.
Once you’re viewing the Story, you can tap to go to the next Snap, tap on the left side of the screen to go back to the previous Snap, swipe left to skip ahead to the next Story, swipe right to go back to the previous Story, swipe down to exit the Story, or swipe up to start a Chat with your friend.
How to create a Custom Story
You can create a shared Story with your friends. Custom Stories can contain up to 1,000 snaps, and they last as long as someone adds a Snap every 24 hours.
- From the camera screen, tap the Profile icon in the top left corner.
- Tap + New Story on the top right.
- Choose to create a Custom Story.
How to use Snapchat Lenses
Want to make your Snaps pop? Apply a Snapchat Lens. They’re a wildly popular format that helps your content stand out. As of July 2021, there are over 2 million lenses to choose from, so you’ll be sure to find one that suits your brand’s style.
Lenses are a special AR effect that’s applied directly to the faces in the Snap. Unlike the creative tools and filters you apply after taking the Snap, you add Snapchat lenses before tapping the capture button. Here’s how:
- Point the camera at your face (with the selfie camera) or a friend’s face (with the front-facing camera). You can include multiple people in your Snap if you choose.
- Tap on one of the faces on the screen. Lenses will pop up at the bottom.
- Scroll through the available lenses to preview the effects.
- Some lenses have prompts like “open your mouth” or “raise your eyebrows.” Once you follow the prompt, your Snap will take on a new form.
- Once you find a lens you like, tap the capture button to take a picture or hold down the capture button to take a video.
How to use Snapchat Filters
To access Snapchat filters, swipe left or right on your Snap. The available filters include color effects, holiday graphics, timestamps, or Geofilters based on your location. In addition, you can press the stack icon that appears under the other creative tools to apply multiple layers of filters to your Snap.
How to use Snapchat on your computer
Snapchat is developed for iOS or Android devices, which means the app isn’t really built to use on a PC or Mac. For example, there’s no web application Snapchat that has a login for you to browse Snaps and Stories on a desktop—unlike Instagram, Facebook, and even TikTok.
However, if you’re adamant about learning how to use Snapchat online, there is a workaround.
How to use Snapchat on PC
It’s tricky, but you should be able to get Snapchat up and running on your PC. Here’s how:
- Open up a new tab in your chosen web browser.
- Head to the Bluestacks website, download their Android emulator (an .exe file) and install it on your PC.
- Once installed, open Bluestacks and double click on the Google Play Store icon, and sign in with your account information.
- Search for Snapchat. It should be the first result you see in the drop-down menu.
- On the Snapchat app landing page, click the Install button.
- Once Snapchat is installed, click Open to launch the app in Bluestacks.
Have trouble using Snapchat on your PC? You might get an error message saying that something has gone wrong. This isn’t an issue with your Google Play account; Snapchat is in the process of clamping down on emulators using its app, so you might just have to bite the bullet and use a smartphone for your Snaps.
How to use Snapchat on Mac
Are you looking to use Snapchat on an Apple Mac? Unfortunately, you won’t find the app in the Mac App Store and will have to perform a similar workaround to use Snapchat on your Mac.
- Open up a new tab in your chosen web browser.
- Head to the Bluestacks website, download their Android emulator (a .dmg file).
- Open the .dmg file and go through the installation process.
- Click Open, then Install Now.
- Once installed, open Bluestacks and double click on the Google Play Store icon, and sign in with your account information.
- Search for Snapchat. It should be the first result you see in the drop-down menu.
- On the Snapchat app landing page, click the Install button.
- Once Snapchat is installed, click Open to launch the app in Bluestacks.
If you find that your Mac won’t open Bluestacks, head to Preferences > Security & Privacy > General > Allow Apps. Remember that each time you want to use Snapchat on your Mac, you’ll need to open Bluestacks first.
And that’s it! You’re now more than ready to start using Snapchat and elevate your business. Want more tips? Check out our article on Snapchat hacks to take your skills to the next level.